In 2026, data is no longer just information it is the digital manifestation of your identity, your hard-earned wealth, and your ultimate privacy. In previous generations, people kept their most valuable possessions in iron safes; today, our entire lives are built upon clouds, servers, and digital signals. The question is no longer whether your data is safe, but whether your digital foundation is strong enough to withstand any breach or leakage.
In this new era, we must evolve beyond simple “security” and move toward Digital Fortification. This article explores how you can transform your data into an unshakeable fortress, ensuring your lifestyle remains both elite and secure.
1. Understanding the Architecture of Digital Fortification

Fortification is not merely about setting a password. It is a layered architectural approach. Just as a medieval castle featured high walls, a deep moat, and internal sentries, your digital fortification plan must be multi-dimensional.
First, you must understand your “Data Surface.” Where is your information scattered? It exists in your social media footprints, banking credentials, smart home sensors, and cloud repositories. Bringing these into a unified secure framework is the first brick in your fortification. As you organize this digital life, you will find that precision is required at every turn. For accurate security audits and financial planning, you can utilize tools like Free Calculators Online, which help you calculate the logic and costs behind your digital infrastructure.
2. The Zero-Trust Model: Trust Nothing, Verify Everything
The golden rule of security in 2026 is “Zero Trust.” This model operates on the principle that the system trusts no one not even devices already inside the home network.
In a fortified digital ecosystem, every login attempt, every data transfer, and every access request must be continuously verified. This ensures that even if a hacker penetrates your perimeter, they met with a new lock at every single step. This “Assumed Breach” mindset keeps you prepared for the worst-case scenario before it ever happens.
3. Mathematical Precision in Data Security
Data security is not just about software; it is a game of pure mathematics. The encryption algorithms that protect our private messages and financial records are built on complex mathematical equations.
To become a true “Digital Fortifier,” you must respect the power of numbers. Whether you are calculating the valuation of your digital assets or assessing the entropy of your passwords, accuracy is your best defense. To manage these complexities, Free Calculators Online serves as an invaluable platform, providing you with the tools to simplify complicated data into actionable insights.
4. Hardware-Level Defense: Beyond Software
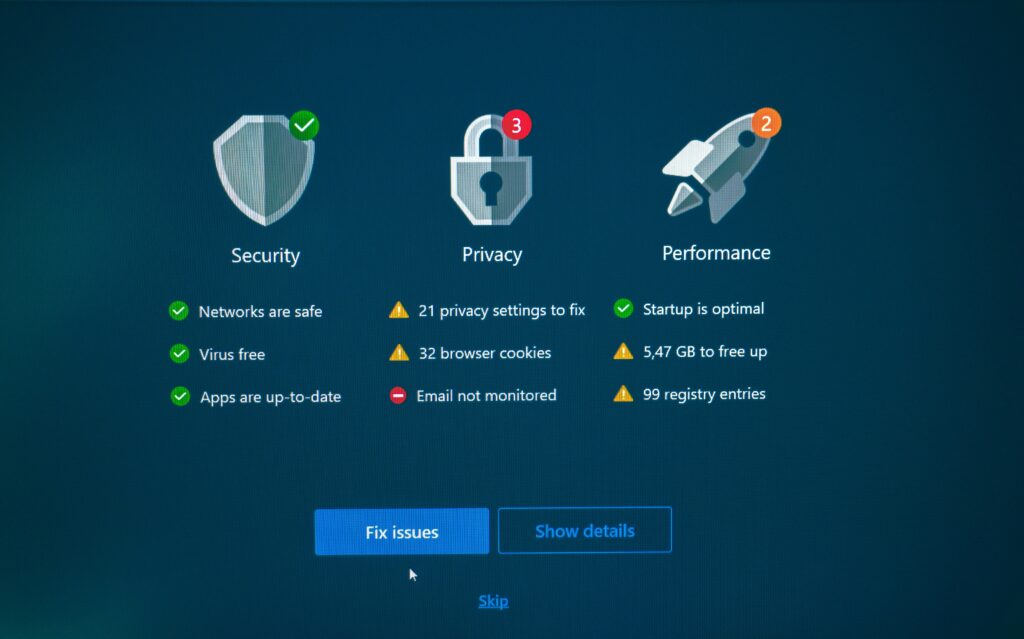
Installing an antivirus is no longer enough. By 2026, sophisticated attackers have moved beyond software vulnerabilities to target hardware itself. Digital Fortification now requires “Hardware Security Keys” and “Biometric Enclaves.”
When your foundation is secured at the hardware level, software bugs cannot easily compromise your privacy. Link your digital identity to physical security tokens items that you, and only you, possess in the physical world. This creates a bridge between the digital and the tangible that is nearly impossible for remote hackers to cross.
5. Managing Your Digital Wealth and Data ROI

Your data is a high-value asset. Just as you track your financial investments, you must audit your data’s “Return on Investment” (ROI) and risk profile. If your data is held by a third-party app that provides no real value, that app is a liability, not an asset.
Regularly auditing your digital assets requires precise calculation. What is the storage cost of your data versus its utility? How much exposure are you risking for a specific service? Using resources like Free Calculators Online allows you to run financial and technical scenarios, helping you decide which digital tools are worth the investment and which ones should be discarded to reduce your attack surface.
6. The Human Factor: The Psychology of Fortification
The weakest link in even the strongest fortress is often human error. Phishing, social engineering, and weak passwords remain a hacker’s favorite tools.
Digital Fortification is incomplete until you shift your mindset to “Security-First.” In 2026, awareness is the ultimate shield. Every link should be questioned, and every service that seems “too good to be true” should be treated as a potential threat. Fortifying your mind is just as important as fortifying your server.
7. Future-Proofing with AI-Driven Defense
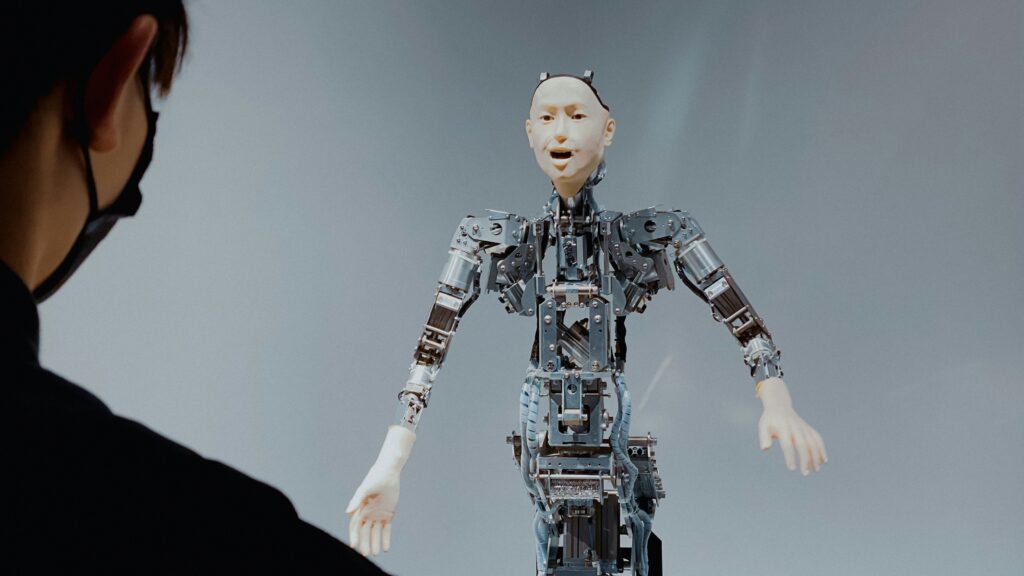
While Artificial Intelligence can be a threat, it is also your greatest guardian. Modern fortification systems utilize AI to detect “anomalous behavior.” If your account is accessed from an unusual location or at an odd time, AI agents can neutralize the threat before you even realize there is a problem.
This proactive approach leads to “Self-Healing Networks” systems that can identify an attack and repair their own vulnerabilities in real-time. This is the hallmark of a truly modern digital foundation.
8. Conclusion: The Peace of Mind Architecture
Digital Fortification is not a burden; it is a premium lifestyle choice. When your foundation is unshakeable, you can navigate the digital world with total confidence. Your data is locked, your privacy is intact, and your digital future is secure.
Always remember that precision and security go hand-in-hand. Calculate every digital move, use the most reliable tools, and keep your foundation updated. For all your daily technical and logic-based challenges, continue to use resources like Free Calculators Online to ensure that every decision you make is data-driven, precise, and protected.
